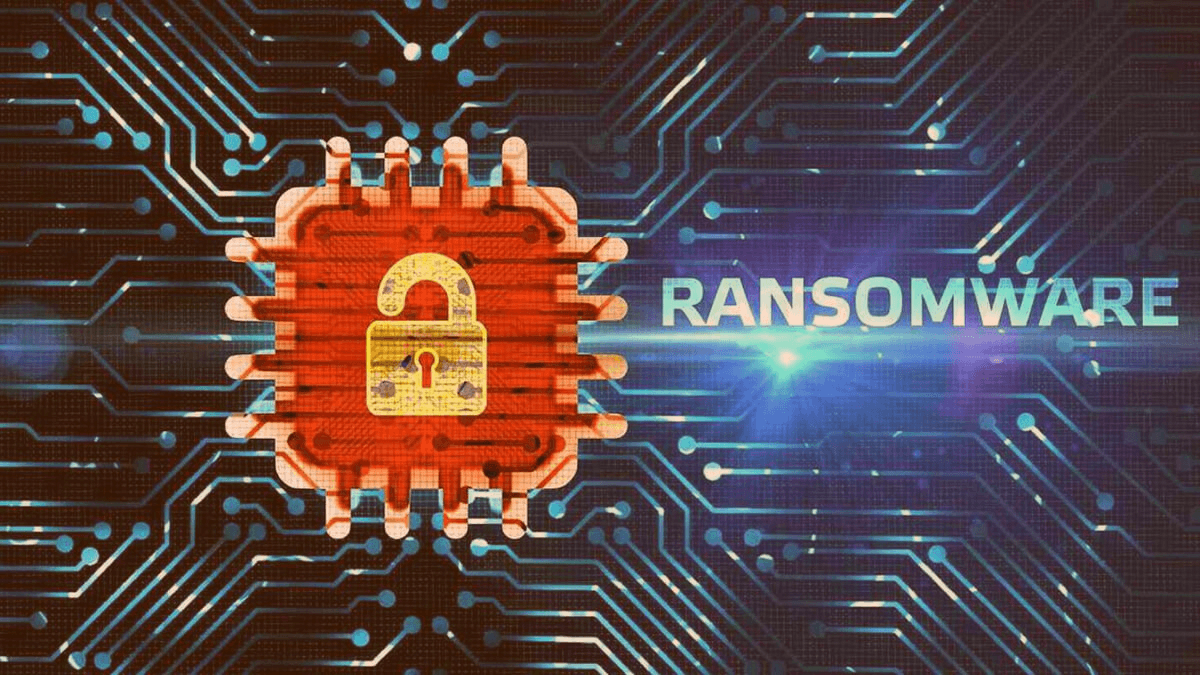
Ransomware in the UAE: Why Local Businesses Are Now Prime Targets – And Whether Your Infrastructure Can Survive an Attack
In October 2023, a well-known logistics company in the UAE woke up to find its entire server environment encrypted. Operations froze. Customer data was inaccessible. The ransom demand arrived within hours — six figures, payable in cryptocurrency.
They paid.
Not because they wanted to. Because they had no other choice. No immutable backups. No tested recovery plan. No segmented network to contain the spread. Just a business that had grown fast and assumed its IT setup was “good enough.”
It wasn’t. And this scenario is playing out with increasing frequency across the region.
The UAE Is Not a Bystander in the Global Ransomware Crisis
There is a persistent misconception among business leaders in the Gulf that ransomware is primarily a Western problem that attackers focus on large American hospitals, European manufacturers, or US government agencies.
The data tells a very different story.
According to the UAE Cybersecurity Council, the country recorded a significant spike in cyberattacks in 2023 and 2024, with ransomware among the most prevalent threats. The UAE’s position as a regional financial hub, its density of multinational operations, and its high rate of digital adoption makes it an exceptionally attractive target.
The Middle East and Africa region saw a dramatic rise in ransomware incidents in the past two years, with UAE based organizations in sectors including logistics, real estate, financial, healthcare, and professional services all reporting breaches.
The question is no longer whether your business could be targeted. It is whether your infrastructure could survive if it was.
Why Most UAE Business Infrastructure Fails Under Ransomware
When we assess IT environments across our client base, we consistently find the same cluster of vulnerabilities. None of them are exotic. All of them are fixable.
1. Flat Network Architecture
Many UAE businesses particularly SMEs and fast-growing firms still operate flat networks where once an attacker gains access to one system; they can move laterally across the entire environment without obstruction. There is no segmentation, no containment. A single compromised endpoint becomes a gateway to everything.
Modern network design for ransomware resilience requires micro-segmentation dividing the network into isolated zones so that a breach in one area cannot cascade across the business.
2. Backups That Cannot Actually Restore You
Virtually every business we speak to says they have backups. Far fewer have backups that work the way they think they do.
Ransomware strains have evolved specifically to target backup systems. Attackers now routinely seek out and encrypt network-attached backup volumes before triggering the main payload.
Resilient backup architecture requires three things:
- Immutable backups — copies that cannot be modified or deleted, even by administrators
- Offsite or air-gapped storage — backups physically or logically isolated from the primary environment
- Tested recovery — regular restoration drills that confirm you can actually recover, at speed, under pressure

3. Unpatched Systems and Unmanaged Endpoints
The entry point for the majority of ransomware attacks is depressingly mundane an unpatched vulnerability, a misconfigured remote desktop protocol (RDP) port, or a phishing email that reaches an employee on an unmanaged device.
In a region where hybrid work, BYOD policies, and rapid headcount growth are common, endpoint sprawl is a real problem. Every unpatched system is an open door.
4. No Incident Response Plan
When an attack happens and the operating assumption for any serious security posture is when, not if the first 60 minutes are critical. How quickly you contain the spread, isolate affected systems, and begin recovery determines whether you lose hours or weeks.
Most businesses in the UAE have no documented incident response plan. No defined roles. No pre-established communication chain. When an attack hits, they improvise at exactly the moment when improvisation is most expensive.
What Ransomware-Resilient Infrastructure Actually Looks Like
Protecting your business against ransomware is not about deploying one magic product. It is about building layered resilience across your entire infrastructure.
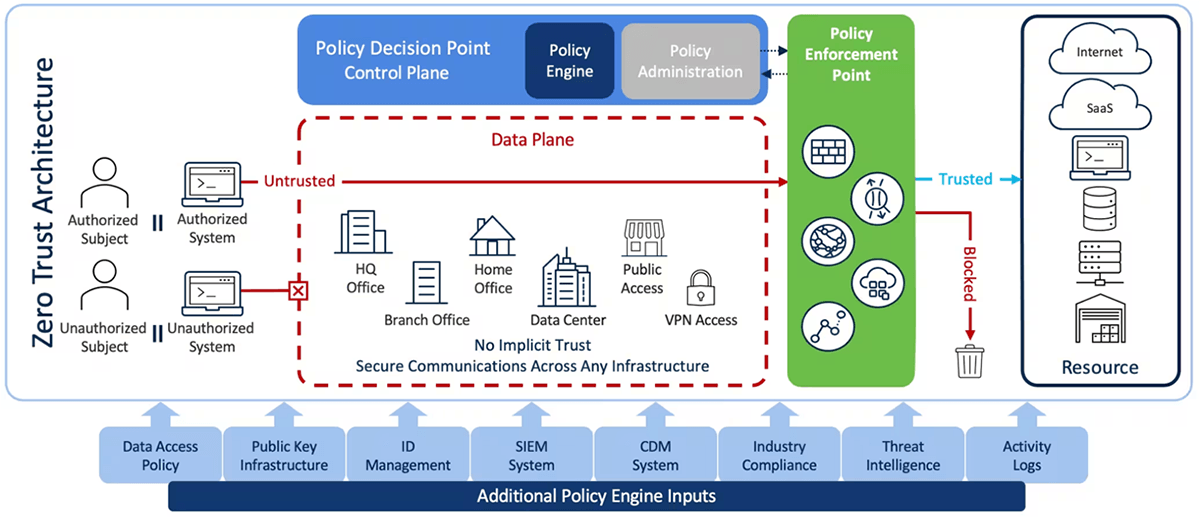
Network Segmentation and Zero Trust Access
Move away from implicit trust within the network. Implement Zero Trust Network Access (ZTNA) principles every user, every device, every connection is verified before access is granted, regardless of whether they are inside or outside the office perimeter.
Immutable, Tested Backup Architecture
Follow the 3-2-1-1 rule: three copies of data, on two different media types, with one offsite, and one air-gapped or immutable. Test restoration quarterly, at minimum.
Endpoint Detection and Response (EDR)
Move beyond traditional antivirus. EDR solutions provide behavioral monitoring that can detect ransomware activity in real time and isolate affected devices before the damage spreads.
Patch Management and Vulnerability Scanning
Implement a structured patch management program. Critical vulnerabilities should be remediated within 72 hours of disclosure.
Employee Security Awareness Training
Phishing remains the number one delivery mechanism for ransomware. A workforce that can identify and report suspicious emails is one of the most cost-effective defenses available.
The Regulatory Dimension: UAE Compliance Is Not Optional
For businesses operating in the UAE, cybersecurity resilience is increasingly a legal requirement, not just a best practice.
The UAE National Cybersecurity Authority (NCA) has established frameworks and controls that apply across sectors. Businesses in regulated industries face specific obligations under the Central Bank of UAE (CBUAE) cybersecurity guidelines. The Dubai Electronic Security Center (DESC) sets requirements for entities operating within the Dubai Government ecosystem.
Building ransomware-resilient infrastructure is not just about protecting operations. In many UAE sectors, it is about meeting your obligations.
A Real-World Baseline: Where to Start This Week
You do not need to transform your entire IT environment overnight. But you do need to start.
| Risk Area | First Step This Week |
| Network Segmentation | Map your current network topology. Identify where lateral movement would be unrestricted. |
| Backup Resilience | Test a full restoration from backup. Time it. Document what broke. |
| Endpoint Security | Audit all devices with network access. Identify unmanaged or unpatched endpoints. |
| Patch Management | Run a vulnerability scan. Prioritize any CVEs rated Critical or High. |
| Incident Response | Name the person who owns the response if an attack occurs tonight. |
The Bottom Line
Ransomware is not an abstract threat to businesses far away. It is active, it is targeted, and it is increasing across the UAE and wider GCC. The businesses that survive attacks and, in some cases, avoid them entirely are the ones that made deliberate infrastructure decisions before an attacker forced their hand.
The logistics company from the opening of this article recovered. It took eleven days, cost significantly more than the ransom they paid, and they lost a major client in the process. They now have immutable backups, a segmented network, and an incident response retainer.
They got there the hard way. You don’t have to.

Let’s Talk About Your Infrastructure Resilience
At Candor, we help UAE businesses assess and strengthen their IT infrastructure and cybersecurity posture from network architecture and backup strategy to endpoint security and compliance readiness.
If you would like an honest assessment of how your infrastructure would hold up under a ransomware attack, speak to our team. We will tell you what we find, not what you want to hear.
👉 Get in touch with our team today.