What the Latest Global Cybersecurity Data Tells Business Owners – And What To Do About It
What the Latest Global Cybersecurity Data Tells Business Owners - And What To Do About It Every year, one of the world's leading cybersecurity companies publishes a detailed analysis of everything that went wrong the attacks that succeeded, the techniques [...]
The Six Questions Every Business Owner Should Be Asking Their IT Team – But Most Never Do
The Six Questions Every Business Owner Should Be Asking Their IT Team - But Most Never Do Most business owners we speak to have the same relationship with their IT setup they trust it is fine because nothing has gone [...]
On-Prem Servers Are Now Resting: A Real Story About Business Continuity, Geo-Redundancy, and What Happens When the Internet Goes Down
On-Prem Servers Are Now Resting: A Real Story About Business Continuity, Geo-Redundancy, and What Happens When the Internet Goes Down A client of ours, a business operating in a region under significant pressure called us some weeks ago with [...]
Cloud Migration in the UAE: What Most Businesses Get Wrong Before They Move
Cloud Migration in the UAE: What Most Businesses Get Wrong Before They Move Picture the scene. A senior leadership meeting somewhere in Dubai. Someone usually the CEO, sometimes the CFO says the words: 'We should move everything to the [...]
When Something Goes Wrong: How to Build an Incident Response Plan That Works Under Real Pressure
When Something Goes Wrong: How to Build an Incident Response Plan That Works Under Real Pressure There is a version of cybersecurity preparedness that ends with the firewall, the antivirus, and the backup schedule. Put the controls in place, monitor [...]
You Can’t Protect What You Can’t See: Why UAE Businesses Need a Vulnerability Assessment Before Their Next IT Investment
You Can't Protect What You Can't See: Why UAE Businesses Need a Vulnerability Assessment Before Their Next IT Investment There is a version of IT security that looks responsible from the outside. Firewall in place. Antivirus running. Backups scheduled. [...]
Ransomware in the UAE: Why Local Businesses Are Now Prime Targets – And Whether Your Infrastructure Can Survive an Attack
Ransomware in the UAE: Why Local Businesses Are Now Prime Targets - And Whether Your Infrastructure Can Survive an Attack In October 2023, a well-known logistics company in the UAE woke up to find its entire server environment encrypted. [...]
Shadow AI Cybersecurity Risks: Managing AI in the Enterprise
Shadow AI in the Enterprise: The New Blind Spot in Your Threat Exposure Strategy Over the last few years, organizations have made meaningful progress in understanding and managing their attack surface. From asset discovery to continuous threat exposure management [...]
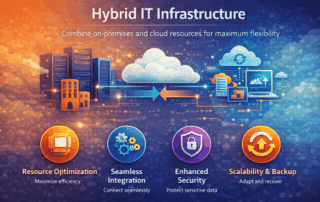
Physical and Virtual Server Deployment: Key Considerations for Modern IT
Physical and Virtual Server Deployment: Key Considerations for Modern IT Why Server Deployment Matters Servers are the backbone of your IT infrastructure. Choosing the right deployment approach physical, virtual, or hybrid affects: Application performance and availability Scalability for future [...]